漏洞概述 | |||
漏洞名称 | Microsoft WordPad 信息泄露漏洞 | ||
漏洞编号 | QVD-2023-24196、CVE-2023-36563 | ||
公开时间 | 2023-10-10 | 影响对象数量级 | 亿级 |
奇安信评级 | 中危 | CVSS 3.1分数 | 6.5 |
威胁类型 | 信息泄露 | 利用可能性 | 高 |
POC状态 | 已公开 | 在野利用状态 | 已发现 |
EXP状态 | 未公开 | 技术细节状态 | 已公开 |
利用条件:需要用户交互。 | |||
01 漏洞详情
影响组件
写字板(WordPad)是简单的文字处理器。自从Windows 95开始,Microsoft Windows大部分的版本都内建了这个软体。它的功能比记事本强,但比Microsoft Word弱。WordPad 的功能发源自于Windows 1.0x时期的小作家。
漏洞描述
近日,奇安信CERT监测到Microsoft WordPad 信息泄露漏洞(CVE-2023-36563),wordpad在解析rtf文件包含的ole对象时会尝试访问Linked object的Topic指向的文件,如果Topic是一个UNC路径则会尝试通过网络访问,并尝试使用NTLM认证,导致泄露NTLM hash。
鉴于该漏洞影响范围较大,并且已经监测到在野利用,建议客户尽快做好自查及防护。
02 影响范围
影响版本
Windows 10 for x64-based Systems
Windows 10 for 32-bit Systems
Windows 10 Version 22H2 for 32-bit Systems
Windows 10 Version 22H2 for ARM64-based Systems
Windows 10 Version 22H2 for x64-based Systems
Windows 11 Version 22H2 for x64-based Systems
Windows 11 Version 22H2 for ARM64-based Systems
Windows 10 Version 21H2 for x64-based Systems
Windows 10 Version 21H2 for ARM64-based Systems
Windows 10 Version 21H2 for 32-bit Systems
Windows 11 version 21H2 for ARM64-based Systems
Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for 32-bit Systems Service Pack 2
Windows Server 2016 (Server Core installation)
Windows Server 2016
Windows 10 Version 1607 for x64-based Systems
Windows 10 Version 1607 for 32-bit Systems
Windows Server 2012 R2 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 (Server Core installation)
Windows Server 2012
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for x64-based Systems Service Pack 2
Windows 11 version 21H2 for x64-based Systems
Windows Server 2022 (Server Core installation)
Windows Server 2022
Windows Server 2019 (Server Core installation)
Windows Server 2019
Windows 10 Version 1809 for ARM64-based Systems
Windows 10 Version 1809 for x64-based Systems
Windows 10 Version 1809 for 32-bit Systems
其他受影响组件
无
03 复现情况
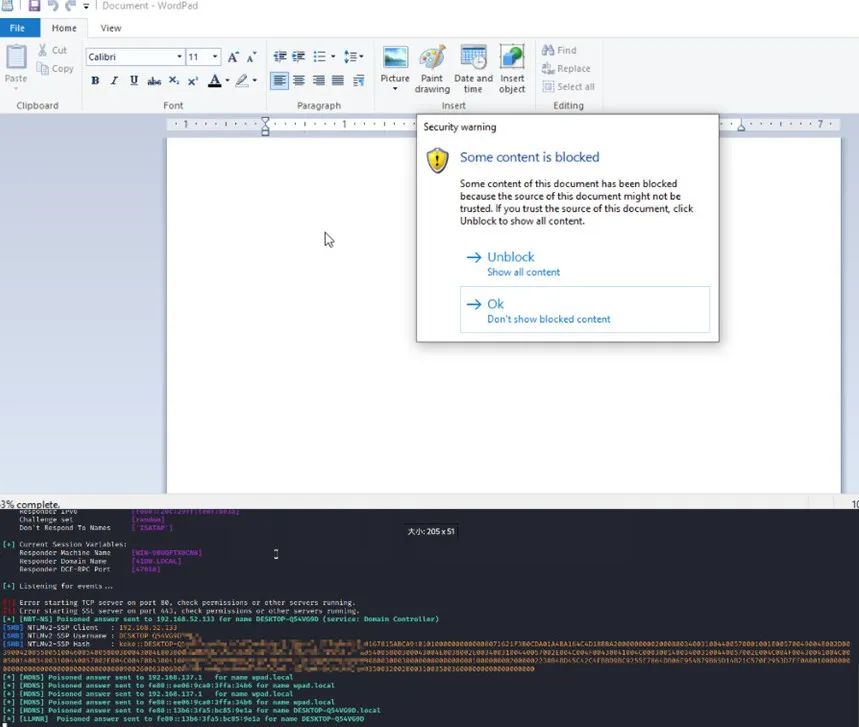
目前,奇安信CERT已成功复现Microsoft WordPad 信息泄露漏洞(CVE-2023-36563),截图如下:
04 处置建议
安全更新
下载对应目标系统的补丁并安装:
https://msrc.microsoft.com/update-guide/en-US/advisory/CVE-2023-36563
缓解措施
设置注册表HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Ole\\AppCompat\\
OLELinkConversionFromOLESTREAMToIStorage,在该项内新建DWORD值Disabled为0x00000001,该项会禁止链接对象的转换,如果已知应用程序不受该漏洞影响,则可以新建REG_MULTI_SZ类型的ExclusionList,并将应用程序名称填入,如Outlook.exe、Winword.exe。
05 参考资料
[1]https://securityonline.info/poc-released-for-microsoft-wordpad-cve-2023-36563-flaw-exploited-in-attacks/
[2]https://www.cert.ssi.gouv.fr/actualite/CERTFR-2023-ACT-045/
[3]https://www.cert.ssi.gouv.fr/avis/CERTFR-2023-AVI-0827/
[4]https://securityonline.info/five-security-vulnerabilities-added-to-cisas-kev-catalog/
[5]https://www.cisa.gov/known-exploited-vulnerabilities-catalog
[6]https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-36563
声明:本文来自奇安信 CERT,版权归作者所有。文章内容仅代表作者独立观点,不代表安全内参立场,转载目的在于传递更多信息。如有侵权,请联系 anquanneican@163.com。
